https://xsolutions.com/wp-content/uploads/2023/01/Passwords-small.jpg
443
788
Joe Imperato, Sr.
https://xsolutions.com/wp-content/uploads/2023/09/XSol-Logo-header-300x138.png
Joe Imperato, Sr.2023-01-26 07:30:002023-01-27 11:00:24Are Your Passwords Compromised?
https://xsolutions.com/wp-content/uploads/2023/01/Passwords-small.jpg
443
788
Joe Imperato, Sr.
https://xsolutions.com/wp-content/uploads/2023/09/XSol-Logo-header-300x138.png
Joe Imperato, Sr.2023-01-26 07:30:002023-01-27 11:00:24Are Your Passwords Compromised? https://xsolutions.com/wp-content/uploads/2023/01/Passwords-small.jpg
443
788
Joe Imperato, Sr.
https://xsolutions.com/wp-content/uploads/2023/09/XSol-Logo-header-300x138.png
Joe Imperato, Sr.2023-01-26 07:30:002023-01-27 11:00:24Are Your Passwords Compromised?
https://xsolutions.com/wp-content/uploads/2023/01/Passwords-small.jpg
443
788
Joe Imperato, Sr.
https://xsolutions.com/wp-content/uploads/2023/09/XSol-Logo-header-300x138.png
Joe Imperato, Sr.2023-01-26 07:30:002023-01-27 11:00:24Are Your Passwords Compromised?


Benefits of Monitoring the Dark Web
Introduction
What people see on search engines, like Google,…
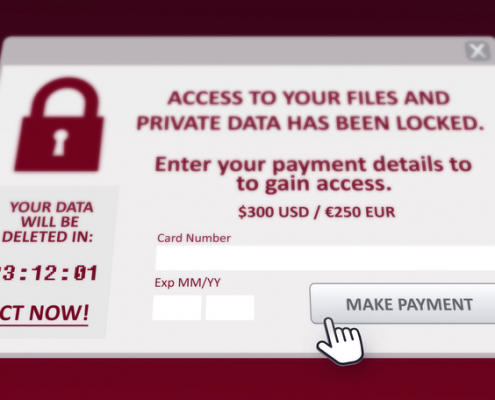
Ransomware's Profit Centers
Ransomware has evolved. Criminals are no longer satisfied with only encrypting your data and asking for money. Find out what the cyber-thieves are up to now.



Deception NEVER Takes A Vacation
Your phone is a target! Thieves create real-looking fake apps and post them in authentic app stores. Do your research before downloading an app.



Security In A Connected World
Wi-Fi and Smart Devices go together. To stay safe, you need to take precautions. Read this post and learn how to take control of your security in an always-connected world.



Your Phone—Always Connected—Always At Risk
Do you use your cell phone to make purchases? Next time, think again. Read Carlos's story to see why.



31 Tips To Keep You Safe
Cybersecurity Awareness Month may be over, but these 31 tips are timeless. Include them into your daily practices. Be safe.



Is Social Engineering Effective?
Social Engineering is the method of choice for hackers. Uber or Rockstar Games learned this the hard way. Learn from these breaches to recognize and prevent being victimized.
A Horror: Cyber Crime!
Scary movies are a staple this time of year. But you can learn from the actor’s “mistakes” and keep yourself safe from cybercrime. Read how.
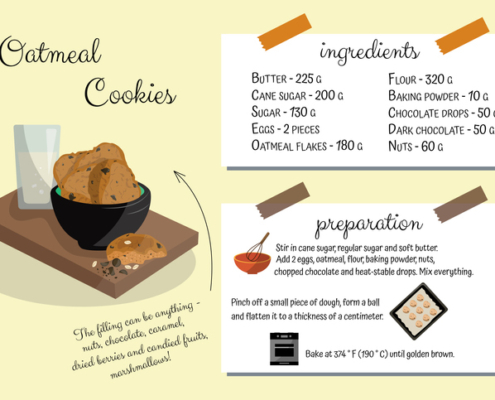
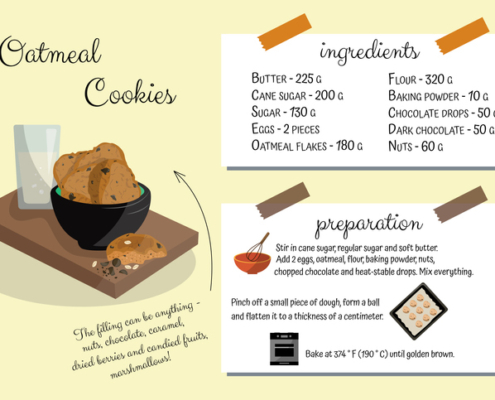
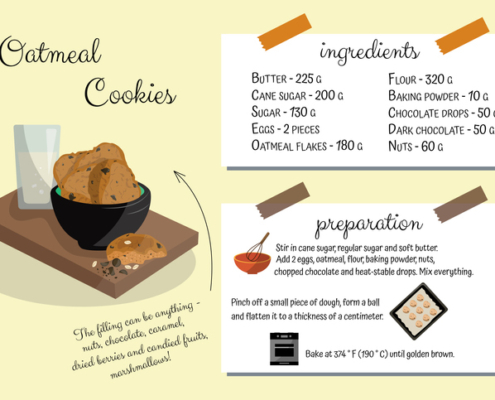
The Recipe for Strong Cybersecurity
Getting protected is like following a good recipe. Use the proper ingredients in the correct order, and you will be more protected than most.



Are Your Passwords Compromised?
Passwords are the digital door to your online life. Be very protective of them and do everything possible to keep them out of the hands of cybercriminals. Here’s how.



Benefits of Monitoring the Dark Web
Introduction
What people see on search engines, like Google,…
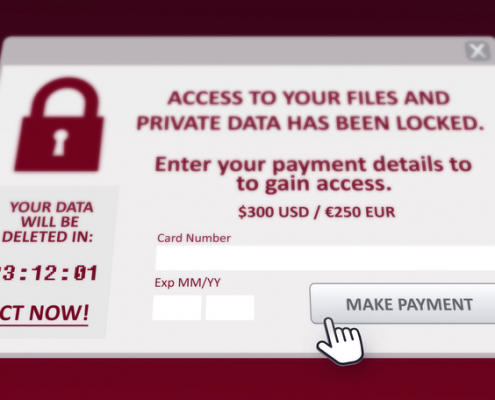
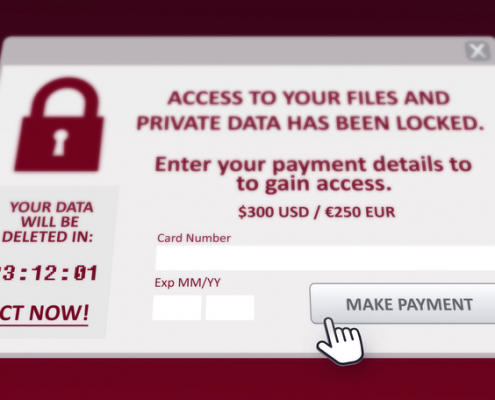
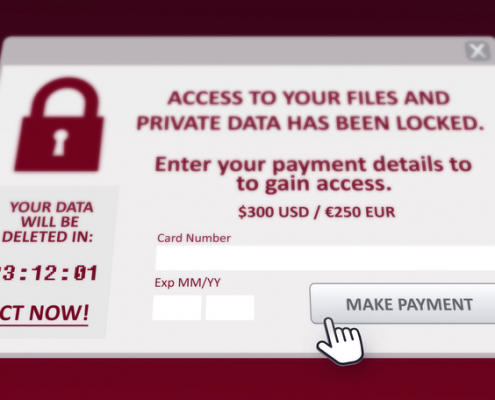
Ransomware's Profit Centers
Ransomware has evolved. Criminals are no longer satisfied with only encrypting your data and asking for money. Find out what the cyber-thieves are up to now.



Deception NEVER Takes A Vacation
Your phone is a target! Thieves create real-looking fake apps and post them in authentic app stores. Do your research before downloading an app.



Security In A Connected World
Wi-Fi and Smart Devices go together. To stay safe, you need to take precautions. Read this post and learn how to take control of your security in an always-connected world.



Your Phone—Always Connected—Always At Risk
Do you use your cell phone to make purchases? Next time, think again. Read Carlos's story to see why.



31 Tips To Keep You Safe
Cybersecurity Awareness Month may be over, but these 31 tips are timeless. Include them into your daily practices. Be safe.



Is Social Engineering Effective?
Social Engineering is the method of choice for hackers. Uber or Rockstar Games learned this the hard way. Learn from these breaches to recognize and prevent being victimized.
A Horror: Cyber Crime!
Scary movies are a staple this time of year. But you can learn from the actor’s “mistakes” and keep yourself safe from cybercrime. Read how.
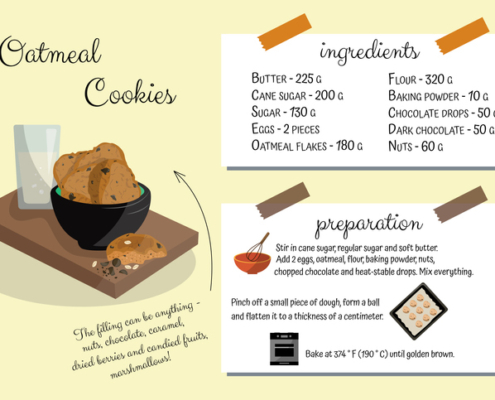
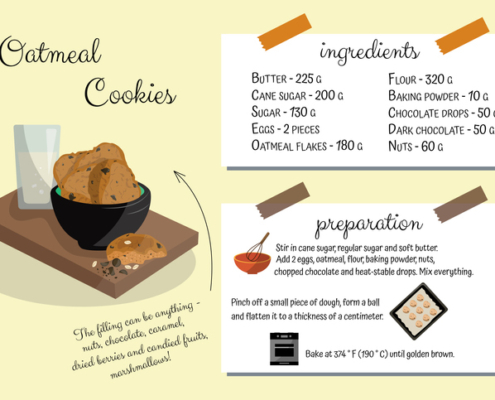
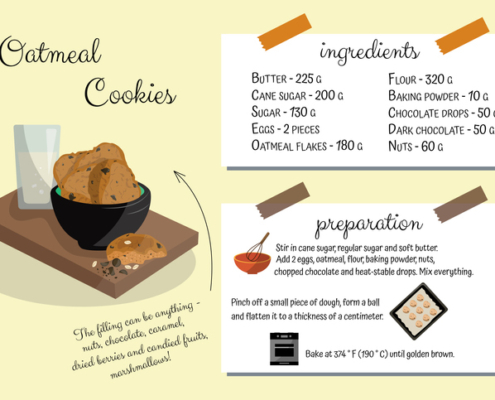
The Recipe for Strong Cybersecurity
Getting protected is like following a good recipe. Use the proper ingredients in the correct order, and you will be more protected than most.
Recent Posts
- Maximizing Business Efficiency with Expert IT Support in Bergen County
- How New York Businesses Can Easily Eliminate Tech Problems
- 6 Common Technology Problems Small Business Owners Face
- Pirates Aren’t Just Threats on the Oceans Blue
- How $43,000 Got Stolen From A Small Business In The Blink Of An Eye
CyberSecurity Tips Newsletter