Security Alert: 23 Million Bogus Emails Spreading Ransomware
In just 24 hours, over 23 million phishing emails carrying the Locky Ransomware virus have been distributed in one of the largest malicious campaigns of the year. The emails have utilized subject lines like:
- please print
- documents
- photo
- images
- scans
- pictures
The emails come with an attachment, this time it’s a ZIP file containing VBS scripts. Once clicked, Locky is downloaded onto the victim’s system, encrypting files, etc. Currently, there are no publicly available keys to unlock this variant.
Beware! As readers of our blog, you know NEVER to click on or open attachments in emails from people or companies you’re not familiar with or that you were not expecting to hear from. Even if an email comes from someone or a company you are acquainted with, it is best that you contact them separately (using their official contact info. Never call a number, etc. published within the email itself) to verify if the attachment or link is legitimate.
96.8% of all malware including ransomware, are distributed via email and can appear to come from anyone, even big name brands or institutions such as the IRS, Dropbox, FedEx, Microsoft, etc.
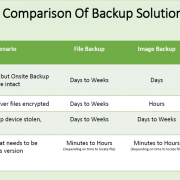
Be aware and don’t become a victim. Make sure your backup system is running properly and that your recent backups are viable. The worst time to find out that they are not working is when you need them the most.
XSolutions is an Elite Partner of Datto, the world leader in Hybrid-Cloud Business Continuity solutions whose systems protect 250+ Petabytes of data with over 800 employees around the globe. Call (845) 362-9675 and let us introduce you to the ultimate defense against data loss—whatever the cause.